Wireshark dissectors overview
Dissectors deode the captured data. As a result of dissection, user is presented with easy to read details of transmitted data. More information about dissectors can be found in Wireshark Developer’s Guide Chapter 9. Packet dissection. During Sharkfest 2013 there was PA 10: Writing Wireshark Dissector presentation.
Data flow between dissectors is shown on figure 1. Each box represents single dissector. In the top part of box there are possible input data source names (dissector source code is in wireshark/epan/dissectors directory). In the middle of the box there is source filename of particular dissector. In the bottom of the box there are possible output data names.
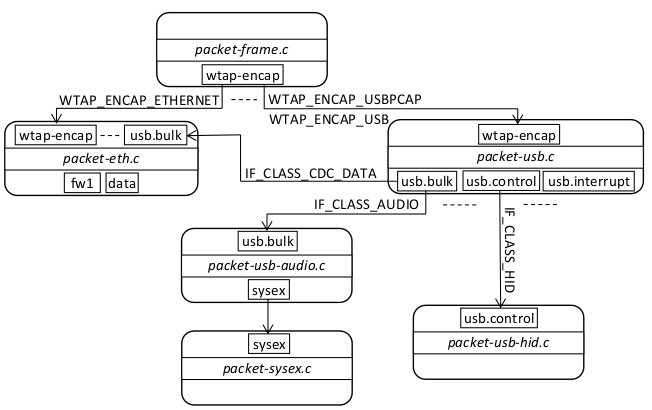 Figure 1: Wireshark dissectors overview.
Figure 1: Wireshark dissectors overview.
packet-frame.c is the top-level dissector that reads pcap files. packet-usb.c knows how to decode the pseudo-headers from Linux (WTAP_ENCAP_USB) and Windows (WTAP_ENCAP_USBPCAP) packets. Moreover packet-usb.c parses USB standard descriptors and outputs the data (bulk, interrupt and control) for additional dissection. In order to make the right dissector process the data (for example, bulk), packet-usb.c should have parsed the USB descriptors to know the USB class the device conforms to. This is why you should plug the device in after starting capture.
Writing USB class dissector
This is not complete guide, for detailed information about how to write dissector check out the Developer’s Guide.
When writing USB class dissector you will be mostly interested in following dissector tables:
- usb.bulk
- usb.interrput
- usb.control
Currently Wireshark does not have dissectors for USB isochronous transfers. To register your dissector for dissecting bulk data of some USB class you call following function:
dissector_add_uint("usb.bulk", IF_CLASS_XXX, handle);
IF_CLASS_XXX is one of the IF_CLASS_ defines from packet-usb.h.
Once you write Wireshark USB dissector it most likely will work out-of-box both with USBPcap traces and Linux USB captures. This was the case for USB Audio dissector. You can view the source code for USB Audio dissector online.